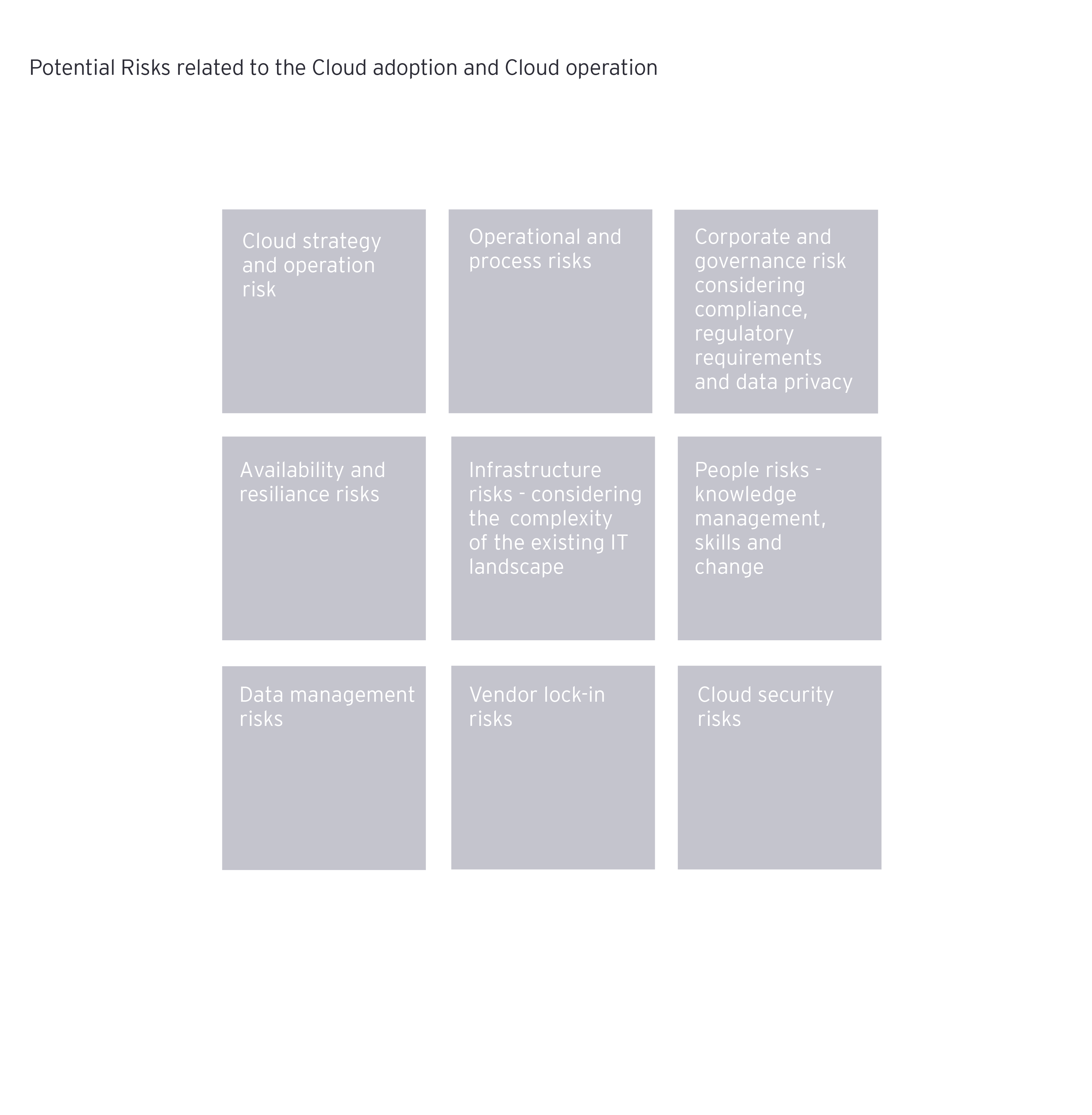
When starting the cloud adoption journey, it’s important to assess potential upside and downside risks. This investment early on improves understanding of how to best govern and manage cloud adoption based on a clear cloud strategy derived from the business (transformation) strategy.
Moving to the cloud does not exclusively affect IT; it also has an impact on IT-supported business processes (and thus operational aspects). A holistic view should be adopted from the beginning. Accordingly, insurance companies face various new challenges in the transformation process. The use of a cloud usually results in changes to the risk map. So it’s vital when evaluating the use of cloud technologies to identify and assess any risks at an early stage alongside the opportunities offered by transformation.
When advising clients on various cloud topics we have noticed different aspects of what could go wrong during the cloud journey:
- Cloud transformation strategy is unclear and/or addressed as pure IT topic. Often missing top management buy-in.
- Organizations fail to manage people risks
- Cloud operation responsibilities are not clearly defined – consider the shared responsibility model.
- Organizations have insufficiently assessed the readiness of in-scope applications leading to the risk that a cloud migration (lift & shift) is executed instead of true cloud transformation.
- Organizations fail to define a cloud security target operating model (TOM).

It often comes back to the fact that the shared responsibility model is not considered enough. Depending upon the cloud service model chosen, responsibilities are shifted. The cloud service provider is responsible for the security of the cloud and the cloud service client is responsible for the security in the cloud.
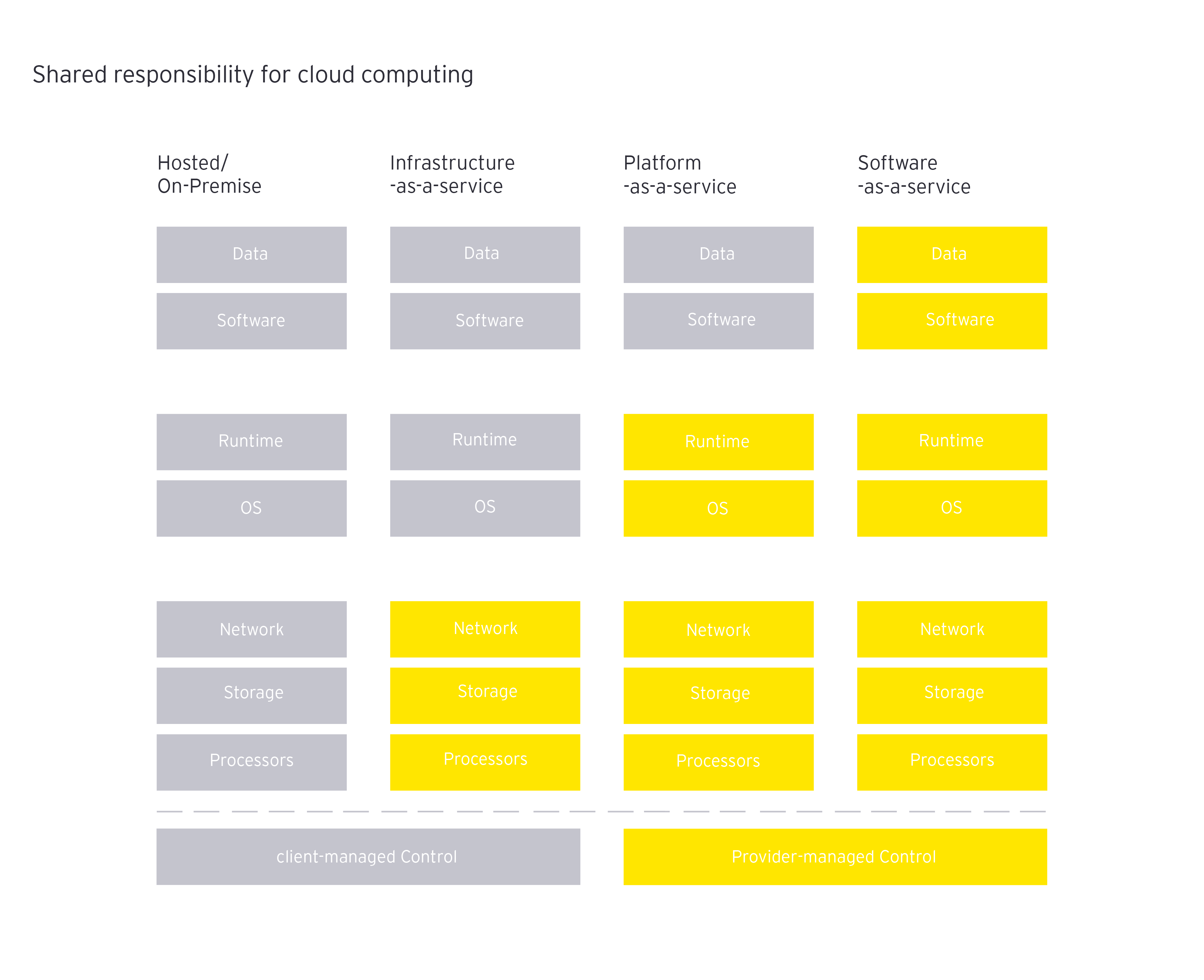
Considering and assessing the existing operating model to securely operate, monitor and govern the future IT infrastructure including core business applications and tools is an important task to be able to define how the target operating model should look.
Focusing on the TOM at an early stage and defining how the cloud-based IT-Infrastructure will be operated and governed – in what will most likely be a hybrid, multi-cloud environment – will help companies to better manage and secure their infrastructure in the future. Other key considerations include having the right tools in place to measure compliance of security controls e.g. database encryption controls or access controls.
Compared with other cybersecurity investments in emerging technologies, cloud computing has overall the highest priority.
What should you consider when defining your cloud (security) target operating model?
All five domains of the NIST Cybersecurity Framework hould be considered when defining security operations. Depending on the cloud service model or combination selected, the following aspects should be considered:
- Identity and access management (IAM)
- Directory services (DS)
- Security information and event management (SIEM), as well as vulnerability and patch management
- Operation of state-of-the art security measures (e.g. web access firewall (WAF), firewall (FW), IDS & IPS, SIEM systems, data leakage prevention)
How can governance over security controls be ensured in a cloud environment?
In addition to the challenge of rethinking and adjusting existing security operations processes, we believe there is a potential risk of outdated security controls during and after transforming to the cloud. These can stem either from inaccurate prioritization or limited resources to update the controls catalogue. Updating controls includes assessing the current controls catalogue to determine if these controls are still appropriate or if new controls are necessary and whether key risk indicators (KRIs) must be adjusted.
Establishing a proper cloud security operations model will also include the definition and implementation of a solid cloud governance solution framework (CGSF). It’s important to build up a solid Cloud Governance Solution Framework (CGSF) to ensure clarity over regulatory compliance, data classification and data governance as well as operation risk management. EY has developed a dedicated financial sector CGSF which allows organizations to lead cloud regulatory controls.
With regard to resilience and business continuity aspects, we recommend repeating the business impact analysis (BIA) considering the cloud-based IT architecture and cloud target operating model. Companies should also reassess existing business continuity strategy options and incorporate cloud-specific measures into business continuity plans.
Key takeaways
A successful cloud transformation journey starts with stakeholder buy-in. Companies should apply a holistic view and consider all opportunities and risks to understand their future security posture in the cloud. It’s important to consider legal and regulatory requirements and address them taking into account all aspects of the business. Finally, your applications and people need to be ready for the transformation. A cloud risk and readiness assessment lays the groundwork for the next steps.
Summary
Having a solid and comprehensive cloud operating model in place, and focusing on security aspects at an early stage of any cloud journey will allow you to protect your most valuable assets, your client data, your intellectual property and to enable options to act fast on the market, to respond to your client needs and to stay client centric providing insurance services to your clients, create trust while transforming and operating your business in secure manner.