
The better the question
How can you ensure 24x7 security of your business data on the cloud?
Ability to detect cybersecurity risks is a priority while migrating on-premise infrastructure to cloud.
A reputed global US$4.5b+ food and beverages company was concerned about security vulnerabilities and wanted to safeguard against current and potential cyber threats. The requirement came to the forefront while transitioning from on-premise infrastructure to the cloud. The transition required integration of many non-native log sources, thereby increasing its security risk exposure.
Besides ensuring a safe transition, the company wanted to build a system which allowed continuous improvement of its security landscape. As a cybersecurity solution, it needed a security operations center capable of designing, transitioning, implementing, configuring, integrating and customizing its cybersecurity strategy.

The better the answer
EY built a managed security operations center for the company
A managed security operation center proactively detects and minimizes impacts of an incident.
Evaluating a partner for establishing a security operations center includes an assessment of its experience and capabilities. The food and beverages company assessed our incident response management processes, the span of pre-deployment activities for infrastructure and applications, and our experience in conducting similar transitions.
We established a managed security operations center (MSOC) to detect and prevent security incidents. Subsequently, we established MSOC operations to provide 24x7 monitoring of cybersecurity threats, incident response and threat intelligence for the company. The ISO 27001 compliant MSOC deployed EY’s proprietary assets and tools, such as next-generation Cognitive Cyber Center (CCC) and EY Security Governance Services.
The implementation involved deployment of specific use cases as actionable correlation rules within the security information and event management (SIEM) system, coupled with newly created threat intelligence inputs and automatic lookups.
During the course of the engagement, EY helped the client recover from an appliance failure incident by invoking the business continuity plan (BCP) and restoring services after return merchandize authorization (RMA) in a very short span of time.
Different aspects of EY’s MSOC for a global food and beverages company

Source: EY’s cyber security engagement team for a global food and beverages company
Accelerated business growth, diversified assets, and a heterogenous digital environment trigged the need for real-time incident monitoring. The company continues to elevate its cyber security posture through constant evaluation of emerging tools and technologies.
~ Anjan Bhattacharya, Cyber Security leader at EY

The better the world works
EY’s MSOC provides round-the-clock security and support.
The MSOC detects and responds to potential future incidents besides providing valuable threat intelligence.
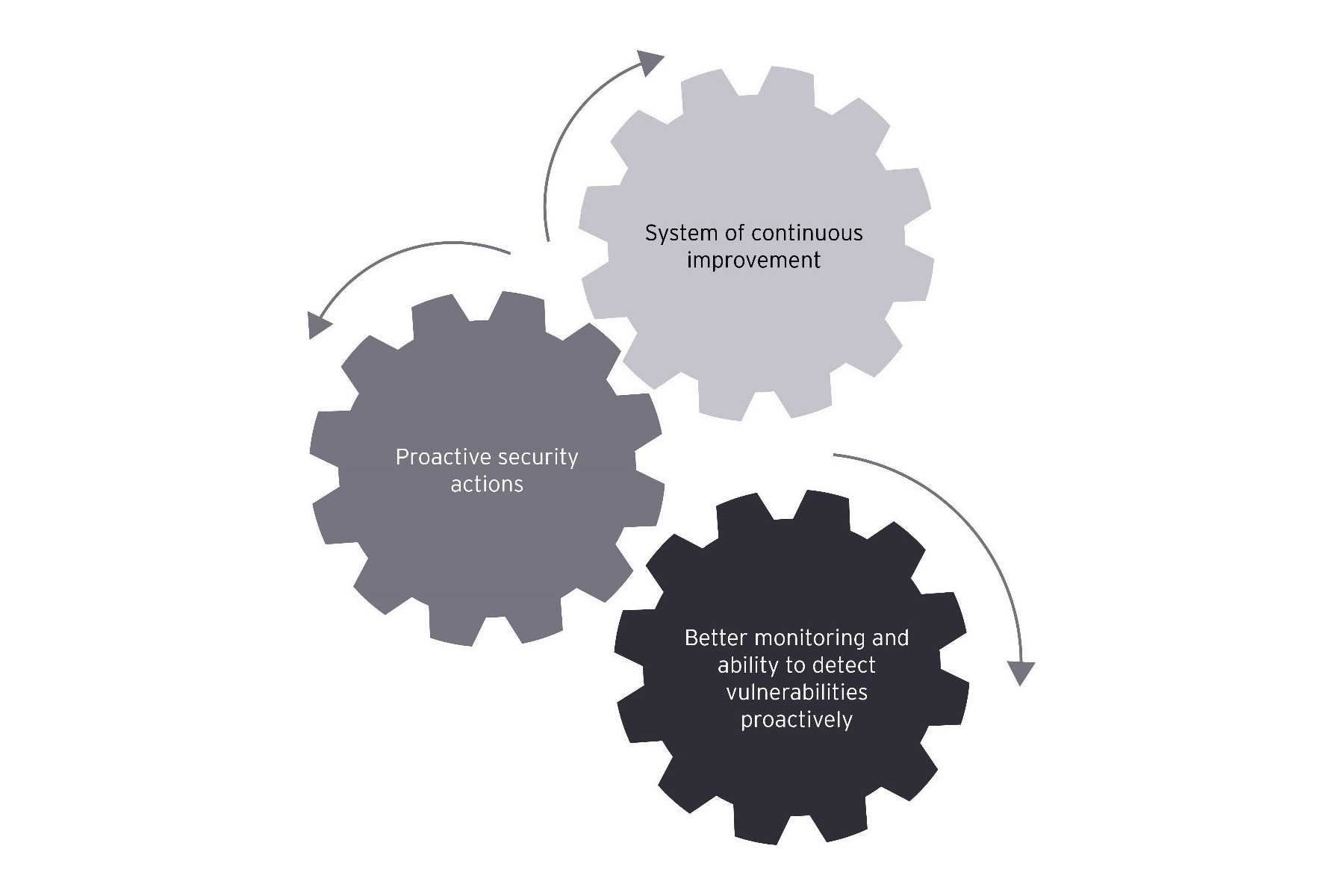
After the deployment of the MSOC, the company could better monitor and improve its ability to proactively detect and minimize the impact of an incident. Independent and expert perspectives provided by the MSOC made the company aware of current information technology security threats and vulnerabilities.
Benefits realized from EY’s MSOC
Source: EY’s cyber security engagement team for a global food and beverages company
Threat advisories issued by the MSOC helps the company take necessary actions proactively. Finally, with the help of the MSOC’s recommendations, it has built an ongoing system of security landscape improvements.

