EY refers to the global organization, and may refer to one or more, of the member firms of Ernst & Young Global Limited, each of which is a separate legal entity. Ernst & Young Global Limited, a UK company limited by guarantee, does not provide services to clients.
Cyber and privacy leaders' agenda
Join the conversation
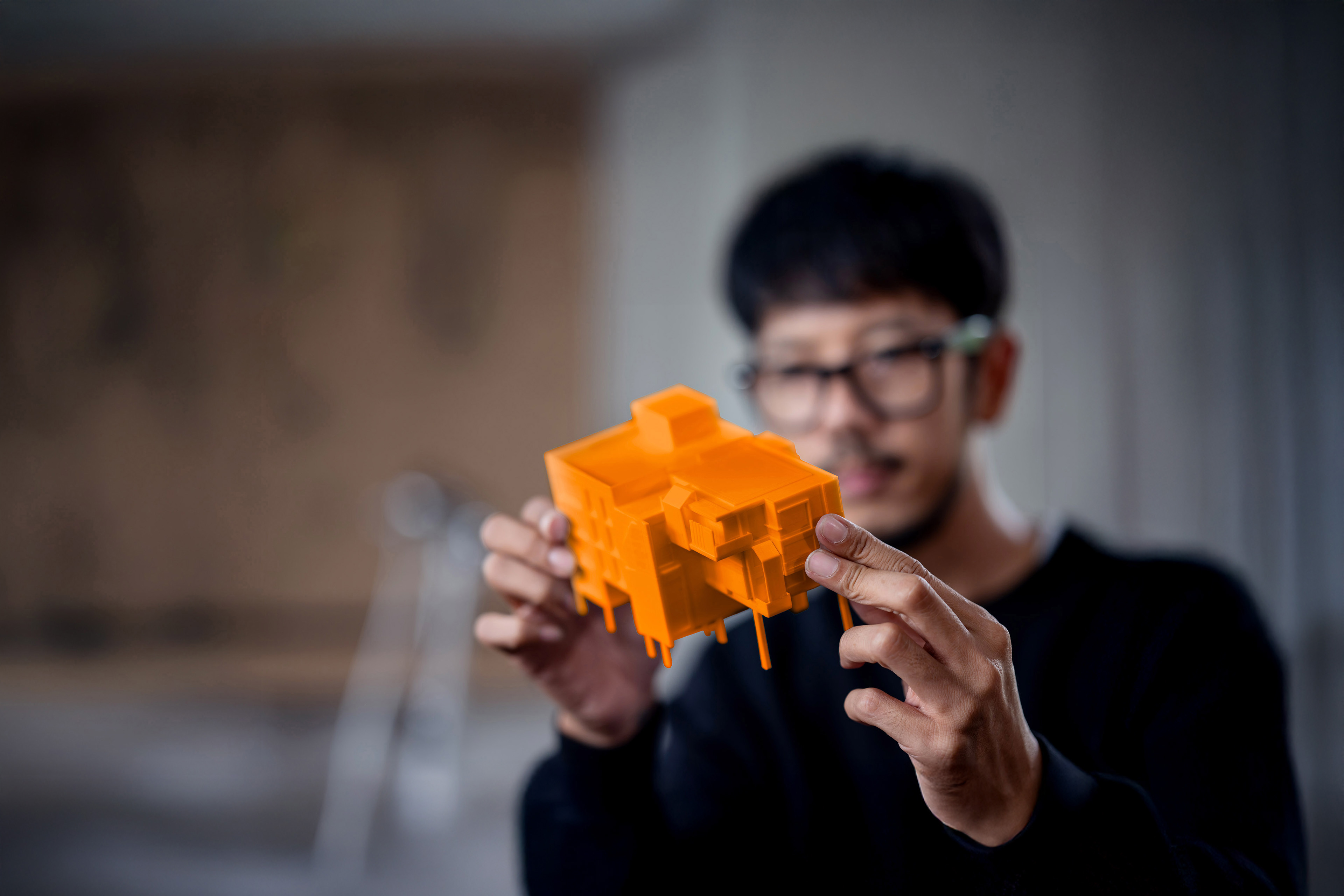
It is harder than ever to stay one step ahead of cybersecurity threats. New, more sophisticated adversaries — some operating autonomously and learning from generative AI models - are thriving in a landscape with multiple attack surfaces opened by hybrid and distributed work, cloud computing at scale, and the digitalization of everything. The stakes are high for CISOs.
"Secure Creators” are redefining cybersecurity in their industries. Secure Creators have fewer cyber incidents, were quicker to respond, and provided 1.5 to 2 times more positive impact on their organization in terms of value creation, innovation and responsiveness to market opportunities when compared to their lower-performing counterparts.
They accomplished this not by simply deploying the right technology, innovating effectively, communicating across their organizations and minimizing attack surfaces, but by executing each of those practices better than their peers.
Here are four actions CISOs can take to better prepare for today and tomorrow:
Cybersecurity leaders are looking to improve capabilities in the following areas:
How EY can help
Discover how EY's Cybersecurity Transformation solution can help your organization design, deliver, and maintain cybersecurity programs.
Read moreService Leader
-
 Richard Watson
Richard WatsonEY Global Consulting Cybersecurity Leader
-
Discover how EY's cybersecurity, strategy, risk, compliance & resilience teams can help your organization with its current cyber risk posture and capabilities.
Read more -
Discover how EY's Next generation security operations & response team can help your organization manage leading-class security operations in a programmatic way.
Read more -
Discover how EY's services & offerings can help your business across multiple aspects of its cybersecurity portfolio.
Read more -
Discover how EY's data protection and privacy team can help your organization protect its information over the full data lifecycle.
Read more -
Discover how EY's identify and access management (IAM) team can help your organization manage digital identities for people, systems, services and users.
Read more -
EY Cybersecurity Managed Services offer seamless, strategic security that gives you the confidence to focus on innovation and growth. Find out more.
Read more - Read more
Our latest thinking
When the world shifts overnight, can you operate at the speed of trust?
Risk operating models must become strategy-first, trigger-based and governance-forward. Learn how Risk Strategists are leading the way.
Three strategic priorities for banking CROs in 2026
The EY/IIF bank risk management survey highlights the need for increased agility against diversifying risks. Find out more.
Reimagine your cyber guardrails to accelerate AI value
In a nonlinear, accelerated, volatile and interconnected cybersphere, enterprise-wide AI adoption is safer and faster with cybersecurity guardrails.
How can cybersecurity go beyond value protection to value creation?
The 2025 EY Global Cybersecurity Leadership Insights Study found that CISOs account for US$36m of each strategic initiative they are involved in. Read more.
How to navigate cybersecurity in the AI world
In this webcast, panelists discuss the transformative role of AI in cybersecurity. Register and learn more.
Six steps to confidently manage data privacy in the age of AI
Concerns raised by AI emphasize the importance of managing data privacy proactively. Consider six steps to prepare. Learn more.