Methods of disposition
Our approach to data disposition provides flexibility in complying with privacy and security obligations. This approach employs two methods of data disposition. When a combination of these two methods are used, maximum benefits will be realized.
1. Pre-emptive
When the organization takes proactive method to dispose of sensitive data through deletion, de-identification or aggregation before it propagates across systems.
2. Disposition on demand
When requests come in from the business or as a result of privacy obligations (e.g., consumer right to be forgotten) for data deletion, the organization begins the process of disposition and responds to the request within the stipulated period of time.
Strategic considerations for data disposition
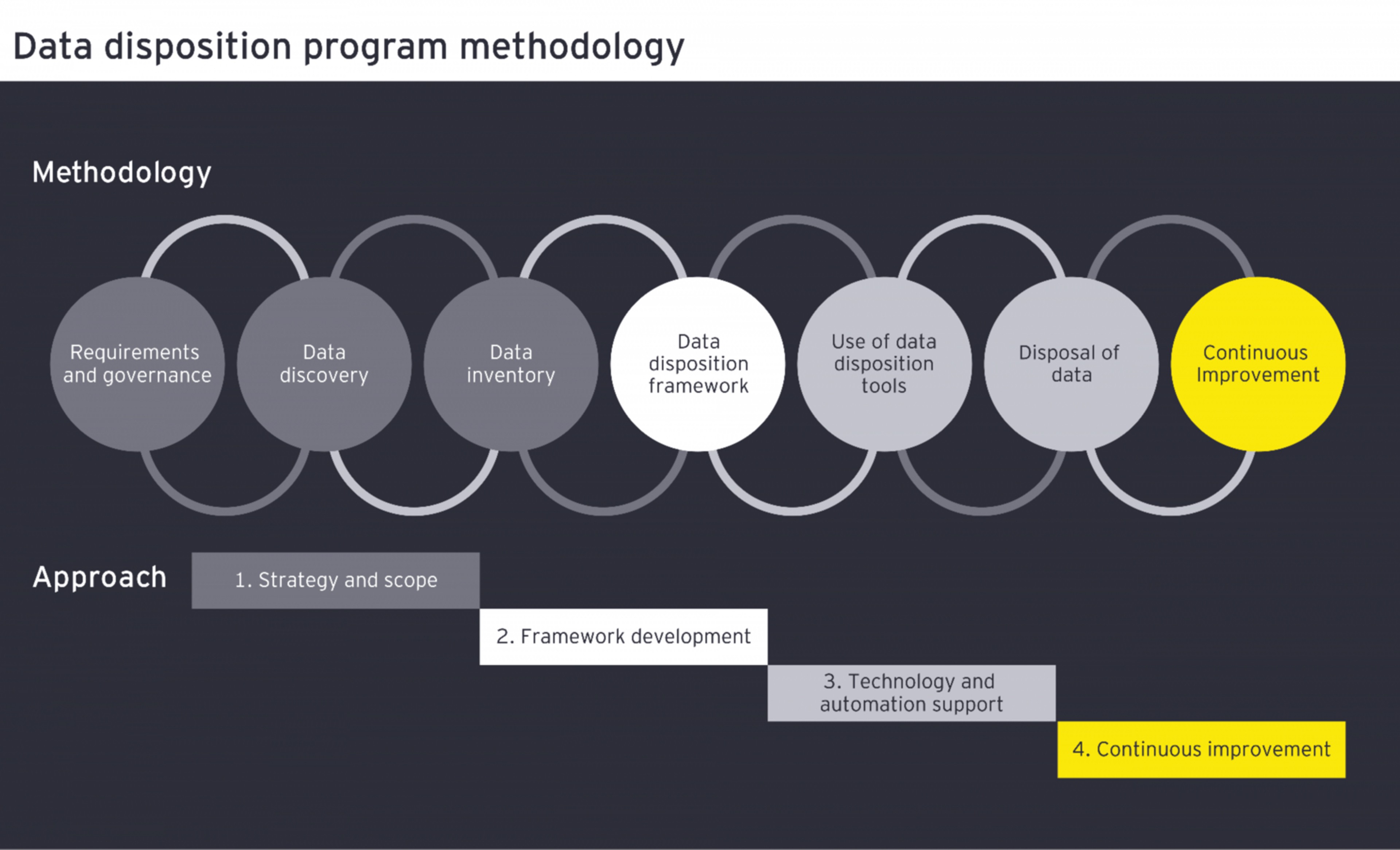
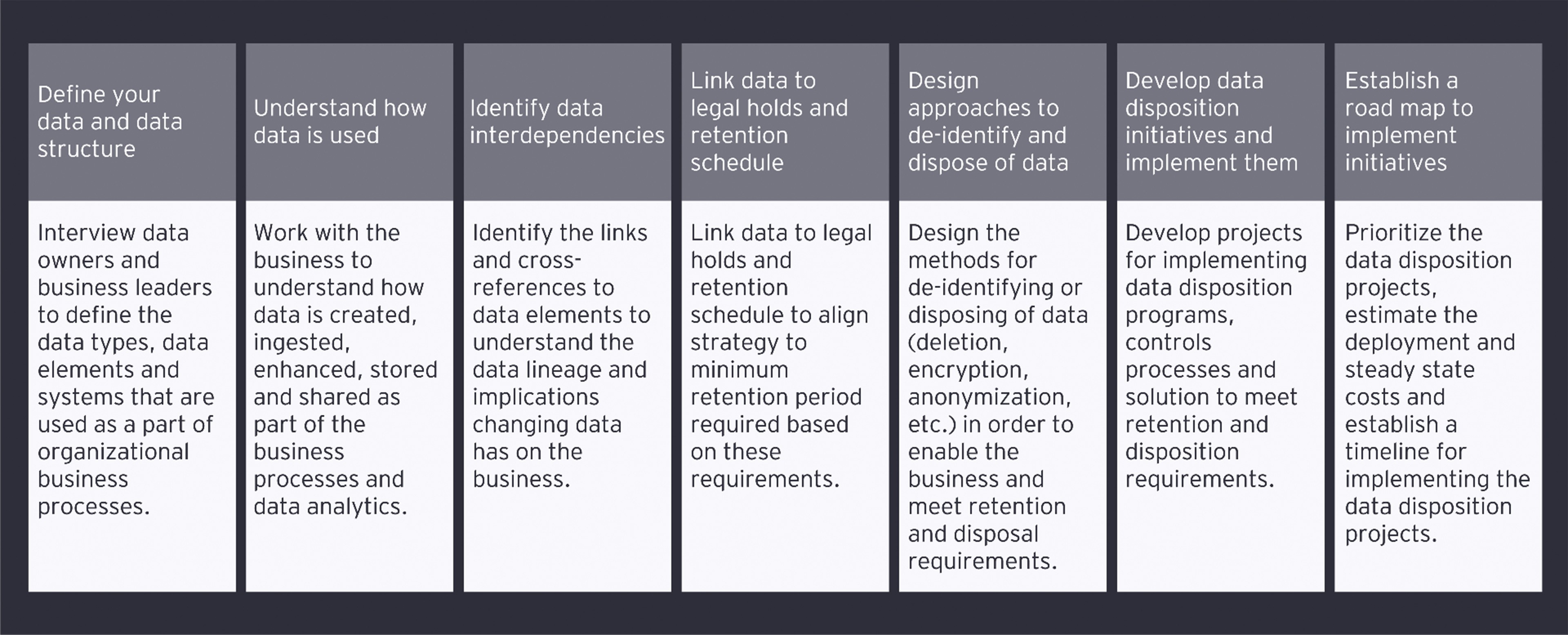
Building a robust and holistic data disposition program requires strategic decisioning and considerations as well as input and integrations with a variety of key stakeholders.
Disposing of data requires data owners, compliance, legal, IT and cybersecurity to work together to develop a strategy that enables the business while meeting data disposition and retention requirements. This strategy is what creates the building blocks for a client’s data disposition program and is outlined below.