
The better the question
How can an organization employ machine learning in cybersecurity?
AI/ML adoption holds the key to robust internal security amidst the evolving cyber threat landscape.
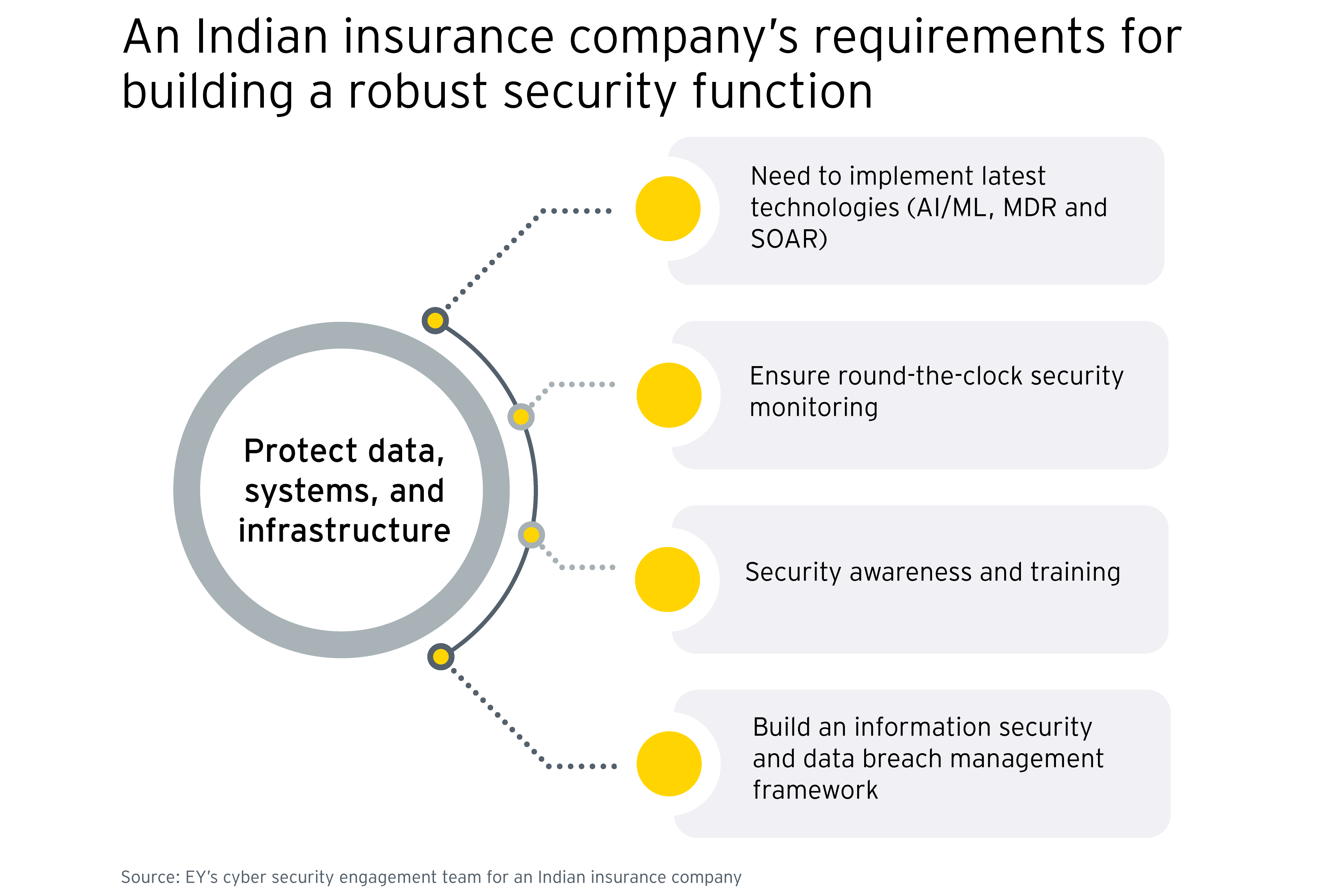
An Indian insurance company was looking to augment its internal security to protect its data, systems, and infrastructure from potential cyber security threats. In addition, the company determined that it needed a 24×7 security log monitoring system that could operate 365 days a year along with the capability to conduct analytics, threat profiling, correlation and alerting.
To build a reliable cybersecurity function, the company determined that it had to implement the latest technologies such as AI/ML, managed detection and response (MDR) and security orchestration, automation, and response (SOAR). To achieve that, it required support from a reliable partner capable of building an information security and data breach management framework and providing device and technology management support.
The company was also looking for support from a partner proficient in information security training and awareness to develop a security awareness program for the organization.

The better the answer
AI/ML enabled cybersecurity is feasible through managed security services
A managed security services (MSS) model monitors and reports threats for proactive action.
For AI/ML enablement, the company was looking for a reliable partner to deploy and operate the required capabilities. The company evaluated several parameters of a service partner, such as its vulnerability management capabilities, knowledge about the organization’s attack surface, and the presence of an established incident management process. As a reliable partner, EY established an MSS model at the company providing round-the-clock security monitoring and incident reporting.
As part of the deployment, EY implemented a security incident and event management (SIEM) process along with maintenance and integration. The solution was equipped with AI/ML capabilities which enabled the company to proactively monitor threats and determine response plans for cyber security breaches. The MSS model offers services through its Cognitive Capability Center (CCC), security governance services, and vulnerability management services.
EY also developed a security awareness program for the company offering training and awareness on cybersecurity. The MSS implementation is compliant with various industry and quality standards, including ISO 27001, OWASP, SANS and NIST.


The better the world works
The AI/ML-enabled MSS proactively manages cybersecurity
The AI/ML-enabled MSS model provides comprehensive threat response and manages several non-core security processes.
The MSS model has helped the company secure its devices and information while continuously monitoring security threats. It manages the deployment and ongoing maintenance of the SIEM system and device integration for the company. As a trusted security partner, EY also built standard operating procedures (SOPs) for alert management, incident management, forensics, report management, log storage and archiving, besides devising business continuity and patching plans for the company.
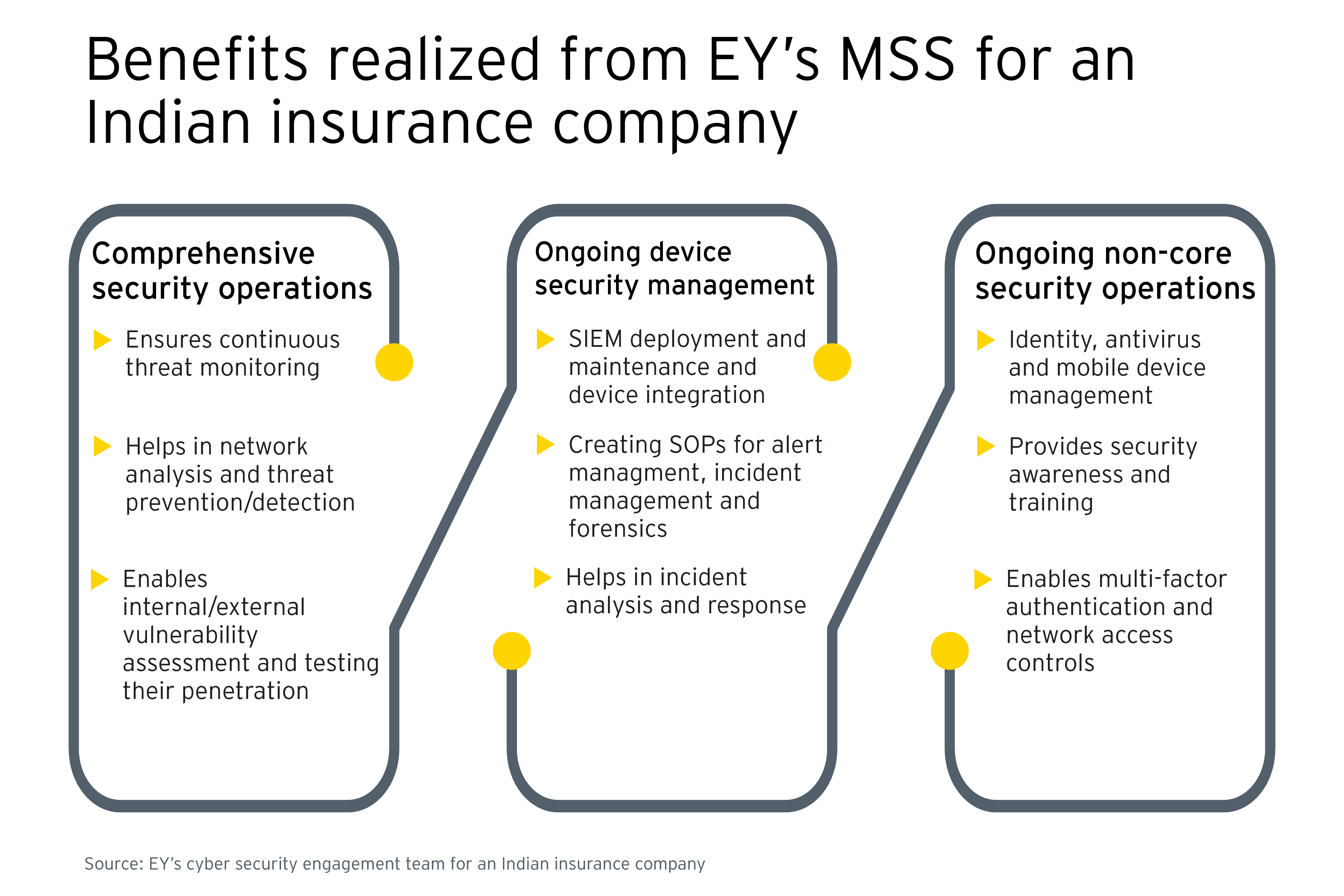
As a result, the company is not only able to prevent active threats, but also conduct analysis on potential vulnerabilities. Besides that, the company has been able to transition multiple non-core parts of the cybersecurity management process to the MSS. These include identity management, antivirus management, mobile device management and intrusion prevention.

